In Today's world, security has become necessary, and software security is one of the most critical aspects. Many web applications exist to make our lives easier and much more enjoyable. We can pay bills online, chat with friends, shop online or communicate with people worldwide. For many of us, web applications have brought convenience, but these applications' perceptions may differ from person to person.
"Software security is about making software behave correctly in the presence of a malicious attack."
It protects information and systems from unauthorized access, disclosure, use, disruption, and destruction. These can be represented through the CIA Triad, as shown below:
Security checks should be made throughout the application project lifecycle to develop secure applications, mainly when dealing with critical information and data.
Security Development Life Cycle Process:
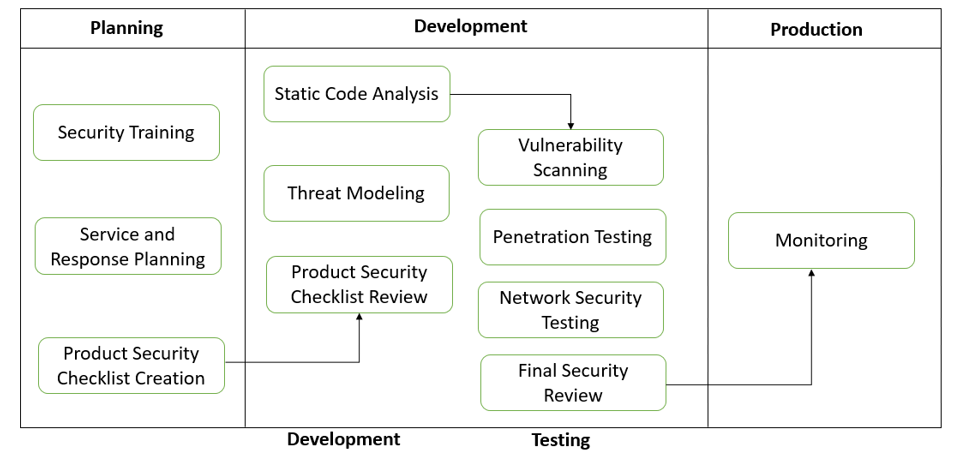
A Secure Development Life Cycle has 3 main phases, i.e., Planning, Development, and Production, which again consists of other sub-phases.
Planning:
- Security Training: This is one of the prerequisites. Some basic concepts for building good quality software include secure design, threat modeling, secure coding, security testing, and best practices surrounding privacy.
- Service and Response Planning: Preparing a security project production service plan and an incident response plan.
- Product Security Requirement Checklist: Prepare security checkpoints as per business requirements; they are majorly divided into 2 categories internal needs and business requirements (B&FS Domain, E-Commerce, etc.)
Development:
- Product Security Checklist Review: The security team reviews the identified checklist and development team and does prioritizations based on feasibility and business needs. The development team identifies standard and reusable components in this security phase.
- Threat Modeling: Potential threats can be identified and organized/prioritized through the Threat modeling process. Threat modeling provides a systematic analysis of the potential attacker's profile, the most likely attack vectors, the assets most desired by an attacker, and a catalog of potential threats that may arise.
- Static Code Analysis: Static program analysis is performed without practically executing the programs. It is also called Source Code Analysis. It is an attempt to highlight possible vulnerabilities within 'static' (non-running) source code. Tool– OWASP LAPSE+
- Vulnerability Scanning: Vulnerability scanning is an automated approach to finding security vulnerabilities in software. These tests can be run as part of vulnerability management by attackers looking to gain unauthorized access.
- Final Security Review: The Final Security Review (FSR) examines all security activities performed on software before the release. This activity includes examining threat models, tool outputs, and performance against the quality gates and bug bars defined during the requirements phase.
Production:
- Monitoring and Process Improvement Plan (Training): Once a problem is identified in a production environment, the security team ensures that the same problem should be addressed only in the planning and design phase. They train resources according to that.
SDL Guidelines in ICT (Information and Communications Technology Industry):
- Authentication and Password Management:
- Validate the user with his identity and ensure he is what he claims to be. Authentication is commonly performed by submitting a username/ID and one or more items of private information that only the user would know.
- Password management system should be designed to store, organize, and encrypt passwords for online accounts on several devices. It is a better and safer alternative to reusing the same two or three passwords.
- Session Management:
- Session management should be implemented as an exchange mechanism that will be used between the user and the web application to share and continuously exchange the session ID.
- Checking URLs in restricted areas, checking exposed Session variables, testing the cookie attribute using intercept proxies, etc., are a few checkpoints in Session Management testing.
- Access Control: It should be implemented to ensure that authenticated users access only what they are authorized to and no more.
Vulnerability Scanning Example:
Here is an example of vulnerability scanning. A vulnerability scanner sends special data to your web application – the type of data that a malicious hacker would send, but it does it safely.
- Vulnerability View: After scanning the web application Checkmarx tool reports 4 "SQL Injection" vulnerabilities.
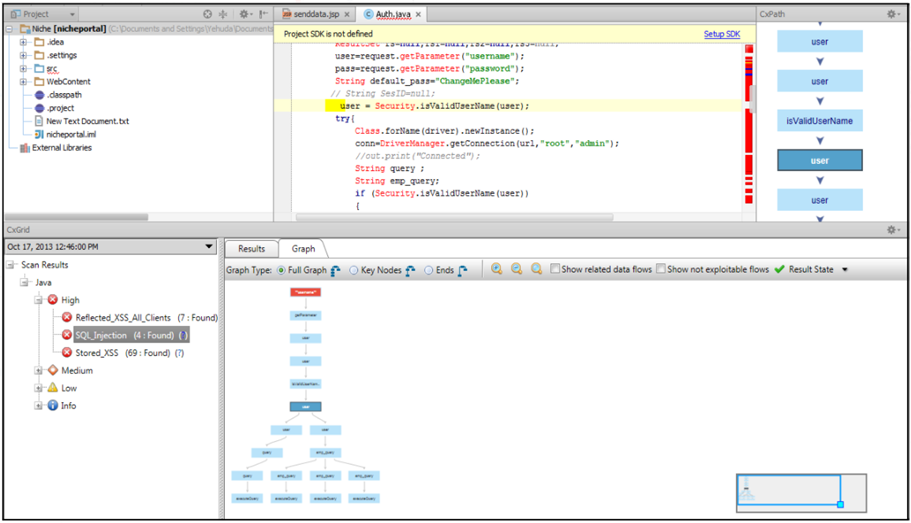
- Result View: This view will show the source code folder, file name, line number, and other details related to other vulnerabilities, which will help development teams to apply fixes at specific locations.
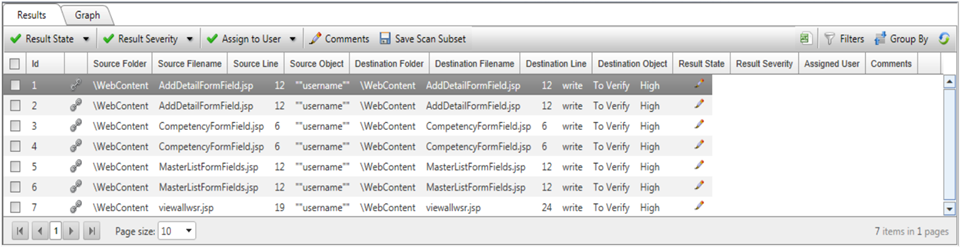
- Once development teams apply fixes, they rerun scans and check whether vulnerabilities are appropriately fixed.
To conclude, see if your organization already follows a secure SDLC process. If not, start now. And if it already does, know that there's always room for improvement! Threats and attacks are evolving daily, and if you are not cautious enough, they may jeopardize your company's reputation and credibility. The best way to keep your software safe from this menace is to implement security measures throughout the development process. Contact Jade experts for your integration needs.













